In our last consul post, we have explained the steps to setup up a multi-node consul cluster which runs on server more.
If you want to use consul services for your application on a server, you need to set up a consul agent on the client mode to talk to the consul cluster. A consul client agent is also a member of the system which can obtain the configurations present in the consul cluster.
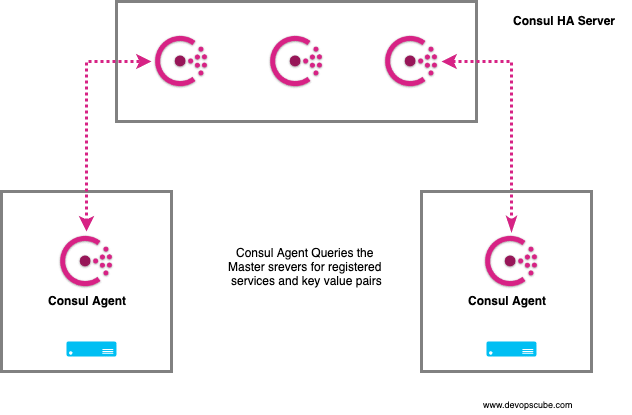
In this post, we will look into the steps involved in running a consul agent on client mode for querying and retrieving services and information from the consul servers.
Install & Configure Consul Agent On Client Mode
Step 1: Update the package repositories and install unzip.
For RHEL/Centos,
sudo yum update -y
sudo yum install unzip -yFor Ubuntu,
sudo apt-get update -y
sudo apt-get install unzip -yStep 2: Head over to consul downloads page. and get the link for Linux 64 bit.
Step 3: Download the consul binary to /opt directory.
cd /opt
sudo curl -o consul.zip https://releases.hashicorp.com/consul/1.4.4/consul_1.4.4_linux_amd64.zipStep 4: Unzip consul binary.
sudo unzip consul.zipStep 5: Move consul executable to /usr/bin directory to be accessible system-wide. You can also move it a location which is in your system path.
sudo mv consul /usr/bin/Step 6: Verify the consul executable by executing the consul command. It should list the available commands.
consulStep 7: Create consul config directories.
sudo mkdir -p /etc/consul.d/client
mkdir /var/consulStep 9: Create a consul config file.
sudo vi /etc/consul.d/client/config.jsonCopy the following config content to the config.json file. You should have the value of encrypt which was used during the consul server configuration. If you don't have this value, you can get it from the consul server from /var/consul/serf/local.keyring file. Also, provide the correct datacenter value available in the consul server
{
"server": false,
"datacenter": "Us-Central",
"data_dir": "/var/consul",
"encrypt": "gsdfHJ3KZvpC/Zsdf9JZSTQQ==",
"log_level": "INFO",
"enable_syslog": true,
"leave_on_terminate": true,
"start_join": [
"10.128.0.3"
]
}Step 11: Create a consul client service file.
sudo vi /etc/systemd/system/consul-client.serviceCopy the following contents
[Unit]
Description=Consul Startup process
After=network.target
[Service]
Type=simple
ExecStart=/bin/bash -c '/usr/bin/consul agent -config-dir /etc/consul.d/client'
TimeoutStartSec=0
[Install]
WantedBy=default.targetStep 12: Reload system daemon.
sudo systemctl daemon-reloadStep 13: Start & check the status of consul client service.
sudo systemctl start consul-client
sudo systemctl status consul-clientStep 14: Check the consul members using the following command.
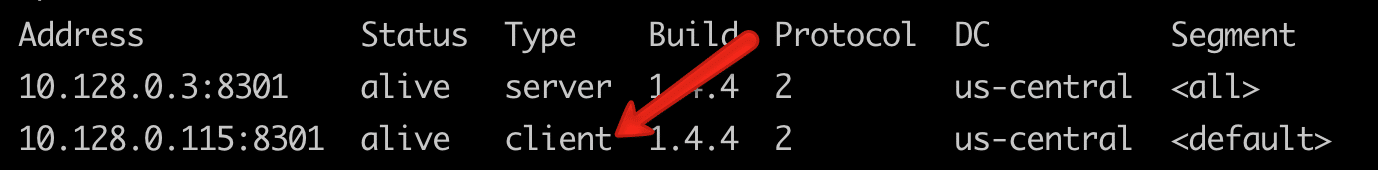
consul membersYou should see your client node in your list of members. It will be of type client. The server cluster members will be of type server.
Query Services & Key Value Pairs From Consul Server
Now that we have successfully configured the client, lets run some checks by retrieving data from the consul server.
List All Available Services
Method 1: Using consul command
consul catalog servicesMethod 2: Using API
curl http://127.0.0.1:8500/v1/catalog/services\?prettyMethod 3: Using DNS query. Here you need to specify your service name to get the details.
dig @127.0.0.1 -p 8600 consul.service.consul SRVQuery key Values From Consul Client
Lets list a key named backend recursively,
consul kv get -recurse backend